A deep dive into the BitTorrent protocol — from .torrent files and tracker communication to peer handshakes and piece assembly.
Decoding the BitTorrent Protocol
Table of Contents:
- Introduction
- The Treasure Map: Decoding the .torrent File
- Connecting to the Tracker: Finding Fellow Adventurers
- The Handshake: Establishing a Connection
- The Bitfield: A Glimpse into the Peer's Inventory
- From Bitfield to Bytes: Navigating the Data Maze
- The Data Symphony: A Chorus of Messages
- The Grand Finale: Assembling the Masterpiece
- Conclusion: The Power of Decentralization
1. Introduction
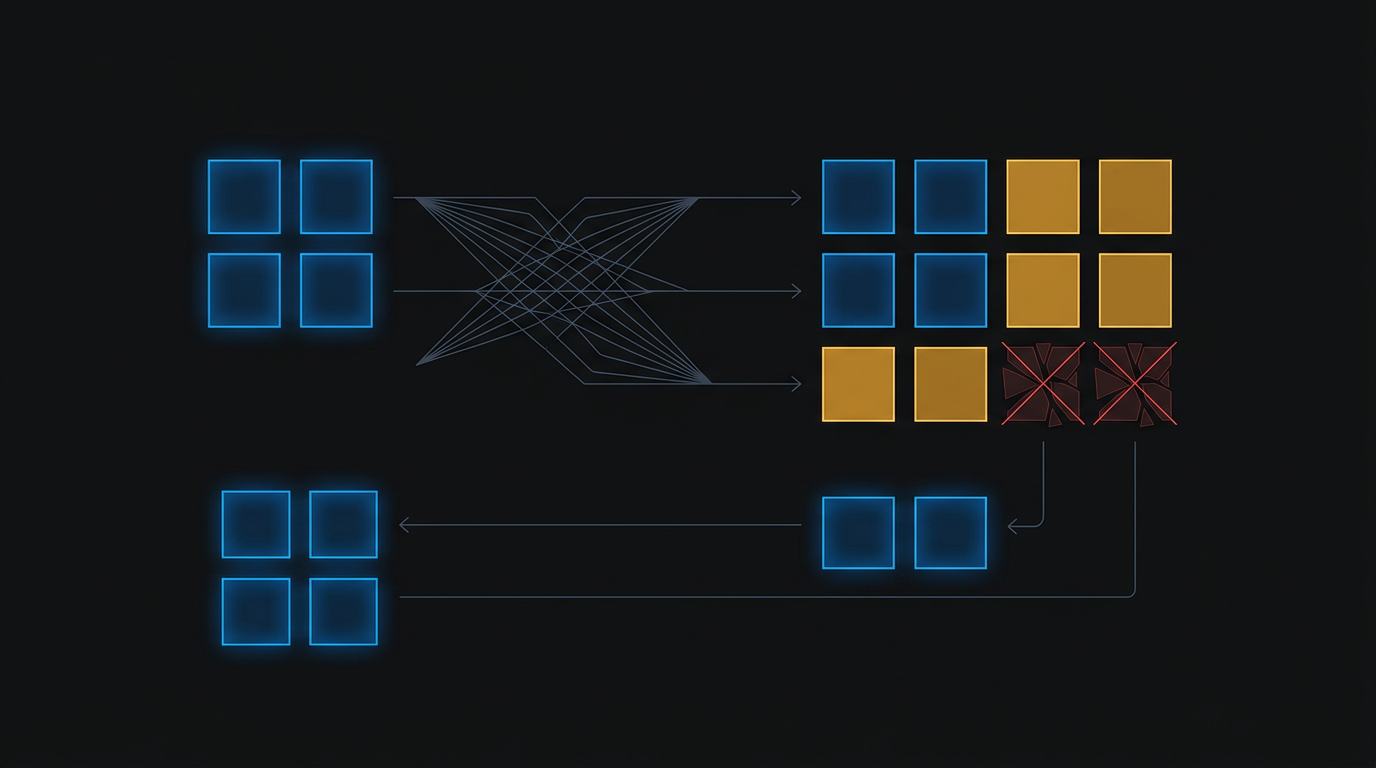
The BitTorrent protocol is a marvel of decentralized engineering, enabling efficient file sharing without the need for central servers. This blog post will guide you through the intricate steps involved in downloading a file using this revolutionary technology.
2. The Treasure Map: Decoding the .torrent File
Our journey begins with a .torrent file, a compact guide containing essential information about the file we seek. This file acts as a treasure map, leading us to the digital bounty:
.torrent file (The Treasure Map)
-------------------------------
Tracker URL: xXx.tracker.land:6969 (Address of a server that helps peers find each other)
Info Hash: d9b6148819fb6760ff1ac2b823b5a239c9153831 (Unique identifier for the file)
File Name: EpicCatVideo.mp4 (Name of the file)
File Size: 10485760 bytes (Total size of the file)
Piece Length: 262144 bytes (Size of each individual chunk of the file)
Piece Hashes: [hash1, hash2, ..., hash40] (Cryptographic fingerprints of each piece)
<details>
<summary>Nerd Info</summary>
- Tracker URL: This URL points to a tracker server, which helps peers find each other.
- Info Hash: This is a unique identifier for the file, generated using a cryptographic hash function.
- Piece Hashes: These hashes are used to verify the integrity of each downloaded piece.
3. Connecting to the Tracker: Finding Fellow Adventurers
Armed with the Tracker URL, our BitTorrent client contacts the tracker server:
Client -> Tracker: "Hello! I'm looking for peers sharing the file with Info Hash d9b61488..."
The tracker responds with a list of IP addresses of other peers currently sharing the same file.
<details> <summary>Nerd Info</summary>- The tracker maintains a list of peers for each torrent.
- It provides the client with a subset of these peers.
- The client can then connect to these peers to start downloading the file.
4. The Handshake: Establishing a Connection
Before exchanging data, we must establish a connection with a peer. This is done through a handshake:
Client -> Peer: "Greetings! Are you a fellow seeker of EpicCatVideo.mp4? My handshake: [pstrlen=19, pstr="BitTorrent protocol", reserved, d9b61488..., MyPeerID]"
Peer -> Client: "Indeed I am! My handshake: [pstrlen=19, pstr="BitTorrent protocol", reserved, d9b61488..., Peer'sPeerID]"
The matching Info Hash confirms they are both interested in the same file.
<details> <summary>Nerd Info</summary>- The handshake message includes the protocol identifier, info hash, and peer ID.
- This ensures both peers are using the same protocol and are interested in the same file.
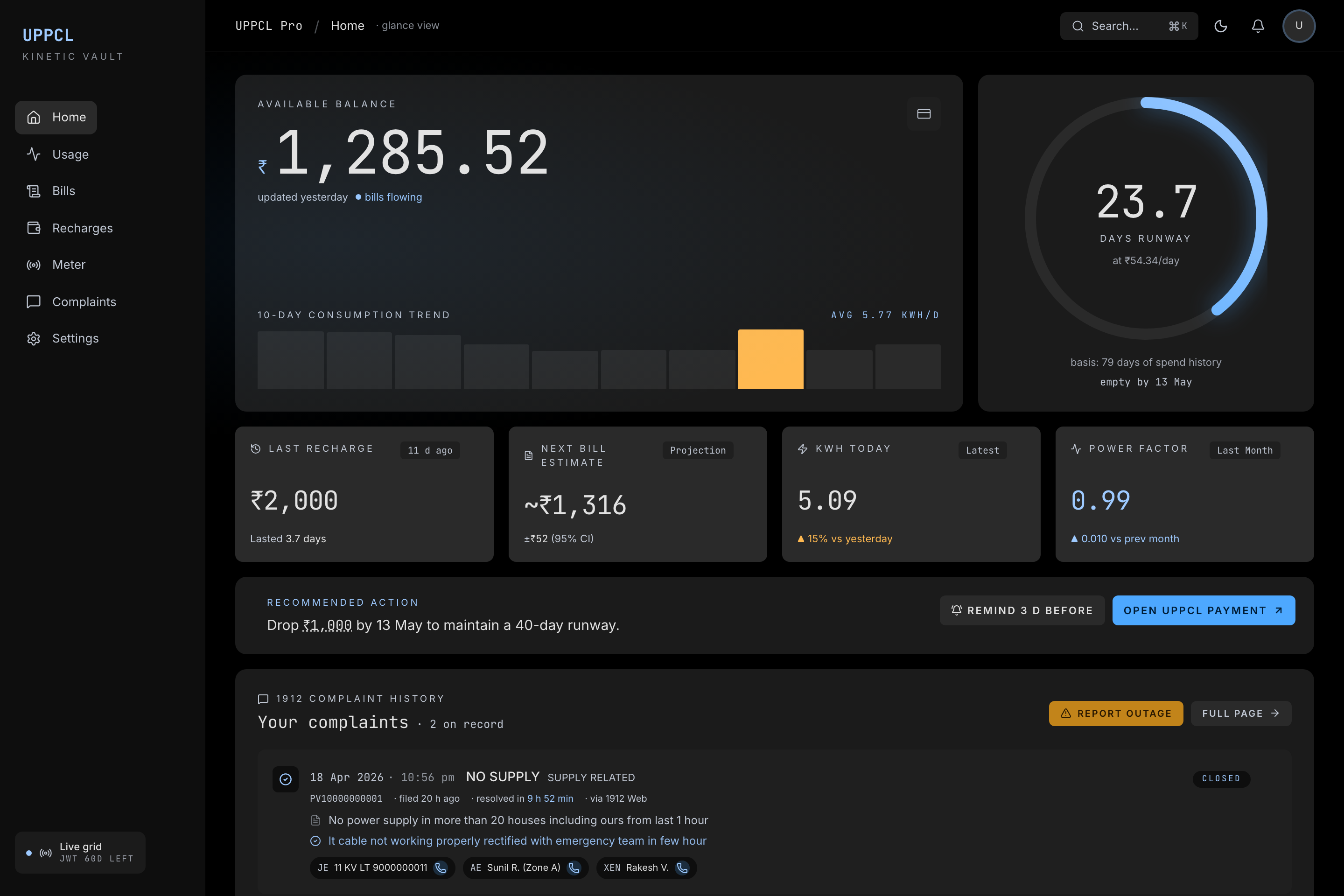
5. The Bitfield: A Glimpse into the Peer's Inventory
Once connected, we need to know which pieces the peer possesses. This information is conveyed through the bitfield:
Client -> Peer: "Show me your inventory! Which pieces of EpicCatVideo.mp4 do you have?"
Peer -> Client: "Here is my bitfield: 110010110101110..." (1 represents a possessed piece, 0 represents a missing one)
<details>
<summary>Nerd Info</summary>
- The bitfield is a compact representation of the pieces a peer has.
- Each bit in the bitfield corresponds to a piece of the file.
6. From Bitfield to Bytes: Navigating the Data Maze
Armed with the bitfield, our client knows which pieces to request. However, it must first navigate the "choke/unchoke" protocol:
client -> peer: "Interested!"
client -> peer: "Unchoke me please!"
peer -> client: "Unchoke"
client -> peer: "Piece 5, from byte 0, 262144 bytes please!"- The "choke" mechanism allows peers to control the rate of data transfer.
- A peer can "choke" another peer to temporarily stop sending data.
- The "unchoke" message grants permission to download data.
7. The Data Symphony: A Chorus of Messages
As pieces are requested, various messages flow between peers:
- Keep-alive: Ensures the connection stays active.
- Choke/Unchoke: Controls the data flow.
- Have: Announces that a peer has acquired a new piece.
- Piece: Contains the actual data of a requested piece.
- These messages are defined in the BitTorrent protocol specification.
- They are used to manage the data transfer and ensure data integrity.
8. The Grand Finale: Assembling the Masterpiece
Piece by piece, the client gathers the fragments of EpicCatVideo.mp4. Each piece is verified against its cryptographic hash. Finally, the complete video is assembled.
- The pieces are assembled in the order specified in the
.torrentfile. - The cryptographic hashes are used to ensure that each piece is correct and has not been corrupted.
9. Conclusion: The Power of Decentralization
The BitTorrent protocol demonstrates the power of decentralized systems. By connecting peers directly, it allows for efficient file sharing without relying on central servers.
Written by
Harshit Chaudhary
Backend Software Engineer at BrowserStack, architecting AI accessibility agents covering 40+ WCAG criteria across web, mobile, and design. Building AI accessibility agents at BrowserStack.